Written by Dr Shalen Sehgal | Crises Control
An alert is not a response.
This distinction sounds obvious. But it is the gap that most crisis management software sold to energy companies today still fails to close.
When the Colonial Pipeline was shut down in May 2021, the DarkSide ransomware group did not bring the pipeline to its knees by overwhelming operations technology. They encrypted the billing systems. The pipeline’s IT infrastructure could not function. Unable to verify transactions, Colonial halted 5,500 miles of fuel flow serving 45 percent of the US East Coast’s supply. A compromised VPN password on an inactive account with no multi-factor authentication was all it took.
What followed was not a failure of detection. It was a failure of coordinated response. The alert had fired. The incident was known. What the organisation then had to do, reach the right people, make decisions under pressure, communicate with regulators, manage a public situation, and document everything in a format that held up to legal and government scrutiny, was something the technology in place was not built to support.
An alert tells you something is wrong. Crisis management software has to tell everyone what to do next, assign who does it, track that it happened, and prove it afterwards. That is a different product category entirely.
The Energy Sector’s Threat Landscape Has Outgrown Alert-Only Systems
The energy sector is not experiencing a temporary spike in incidents. It is in the middle of a structural shift in the volume, sophistication, and variety of threats it faces, and traditional alert-only tools cannot keep up
In 2024, Check Point Research documented 1,162 cyberattacks on utilities, a 70 percent year-over-year increase. A Sophos survey of 275 energy sector IT leaders found that 67 percent had suffered a ransomware attack in the preceding twelve months. IBM’s 2025 X-Force Threat Intelligence Index reports that the energy sector accounted for 10 percent of all incidents in 2024 globally. The August 2024 ransomware attack on Halliburton, the world’s second-largest oil services company, cost the firm $35 million as the breach forced it to shut down IT systems and disconnect customers.
And that is before the physical and environmental incidents. Pipeline ruptures, refinery fires, grid outages from extreme weather, equipment failures at substations. NERC has warned that vulnerable points on the US electrical grid are growing at approximately 60 per day as digitisation expands the attack surface faster than it can be secured.
The threat profile that energy companies now face requires a response system that was built for complexity, not for simplicity. Alert-only platforms were built to detect and notify. The energy sector in 2025 needs crisis management software that picks up where the alert ends, turning detection into coordinated incident response.
Ransomware attacks on energy and utilities sectors increased 80 percent in 2024 compared to the previous year. The detection systems are not the bottleneck. The response infrastructure is.
The Alert-to-Action Gap: Where Energy Incidents Escalate
Every serious energy sector incident of the last decade has a version of the same story buried in the post-incident review. The alert fired early. The information was available. What failed was the mechanism that was supposed to turn that information into coordinated action.
Industry analysis published by Utility Dive describes the problem with precision: manual processes, limited event and incident tracking systems, and multiple siloed point solutions are common across the energy sector. Complex communications and potentially competing goals across diverse teams from operations, service companies, response organisations and government handicap incident response when efficient communication and coordination are imperative.
This is the alert-to-action gap. It is the space between the moment an incident is known and the moment a structured, coordinated, documented response is underway. In most energy organisations, that space is filled with phone calls, improvised decisions, channel fragmentation across radio, email, and messaging apps, and no single person with a complete picture of what is happening.
The gap itself is not new. What has changed is the cost of it.
What the gap looks like in practice
A substation fire is detected. The alert fires across the SCADA system. The on-call engineer receives a notification. They call the operations centre. The operations centre calls the incident commander. The incident commander starts making calls to figure out who is available, what resources are near the site, and what the regulatory notification requirements are for this category of event.
Meanwhile, the field crew at the site is relaying information back through radio, which reaches a different person from the one making the phone calls. A supervisor has sent a WhatsApp message to a group chat that includes some but not all of the relevant people. Leadership at the regional level has heard there is an incident but does not have the location, the nature, or the current status.
Twenty minutes in, three parallel conversations are happening. None of them are synchronised. Nobody has documented anything. The regulatory clock has started ticking and nobody knows exactly when the incident was first detected.
This is not a worst-case scenario. This is what the average energy sector incident looks like without a platform that bridges the alert-to-action gap.
Five Things Energy Sector Crisis Management Software Must Do Beyond the Alert
For energy companies specifically, the capabilities that separate adequate crisis management software and energy sector crisis response software from inadequate solutions come down to five areas. These are not feature comparisons. They are operational necessities.
- Automated workflow activation without a human in the loop
The moment an incident is flagged, every step of the response that can be pre-designed should happen automatically. Alerts go out across all relevant channels simultaneously, not sequentially. Escalation paths trigger if acknowledgement is not received within a set window. Predefined task lists activate for the relevant incident category.
The reason this matters in energy is shift pattern complexity. The person on the call list at 2pm is not the person on the call list at 2am. A platform that depends on a human administrator to find the right workflow, select the right recipients, and press the right button has already lost time that the incident is actively consuming. Incident response automation means the workflow runs the moment the incident is declared, regardless of who is available to run it.
- Role-based task ownership, not individual-dependent assignment
In an energy company operating across multiple sites with rotating crews, individual-dependent task assignment breaks the moment the named person is unavailable. The right architecture assigns tasks to roles, not names. The task goes to whoever currently holds that role on the active shift, and the system tracks acknowledgement in real time.
When a pipeline integrity event occurs at 11pm and the primary contact is mid-flight, the response does not stall waiting for someone to manually identify who the backup is and reach them through a separate channel. The software already knows. The task is already assigned. The next step is already underway.
- A single communication channel across all parties
Energy incidents involve internal teams, contractors, external agencies, regulators, and in some cases government departments and the public. Each of those parties typically has its own communication channels. During an active incident, that fragmentation is dangerous.
The emergency communication system that coordinates the response needs to function as the single channel through which every critical message flows, regardless of whether the recipient is an internal HSE lead, an external contractor, or a government liaison. Two-way communication through the same platform means that responses, status updates, and confirmations all feed back into the same operational picture. No parallel conversations. No version fragmentation.
- Infrastructure independence from systems the incident may compromise
This is the lesson that runs through every major energy sector cyberattack. Colonial Pipeline’s crisis response was hampered precisely because the IT systems it would normally use to coordinate were the ones the ransomware had compromised. When Saudi Aramco was hit by the Shamoon attack in 2012, it was reduced to phone calls and faxes because the digital infrastructure for communication and coordination was gone.
Crisis management software for the energy sector must run on its own cloud infrastructure, with data centres independent of corporate systems, so that it remains operational regardless of what the incident has done to the organisation’s operational technology or IT environment. If the platform depends on the same network as the systems under attack, it is not a crisis response tool. It is a dependency that fails at the worst moment.
- An automatic audit trail from the first notification
NERC CIP standards, FERC requirements, OSHA PSM obligations, the EU’s NIS2 Directive, and a growing range of energy sector specific regulatory frameworks all have one thing in common: after any significant incident, they require documentation. Not documentation assembled from memory and message threads after the fact. A contemporaneous record of what happened, who was notified, what actions were taken, and in what sequence.
A platform that logs every alert sent, every task assigned, every acknowledgement received, and every escalation made, with timestamps, creates that record automatically as the response unfolds. The audit trail is not a post-incident task. It is a byproduct of using the platform. When the regulator or the legal team asks for the timeline, the answer already exists. Read more about how crisis management workflows can build this record without adding to the response team’s workload.
Interested in our Incident Management Software?
Flexible Incident Management Software to keep you connected and in control.
The Regulatory Reality Energy Companies Cannot Ignore
The energy sector operates under some of the most demanding incident reporting requirements of any industry. And those requirements are tightening.
NERC’s 2024 and 2025 CIP standard updates introduced expanded requirements around cybersecurity, access controls, and supply chain risk management. FERC’s 2025 CIP audit findings confirmed that compliance gaps persist across the sector, particularly around third-party vendor management and cloud service risks. In Europe, the NIS2 Directive now mandates strong cybersecurity and incident response requirements for electricity network operators. In the US, the Cyber Incident Reporting for Critical Infrastructure Act is moving towards mandatory reporting timelines that will require energy companies to notify authorities within hours of certain incident types, not days.
The documentation obligations that flow from these frameworks are not satisfied by an alert log. They require a structured, time-stamped record of every action taken during the response. That record needs to be accessible, exportable, and formatted in a way that meets regulatory expectations, not reconstructed from informal sources.
This is where the cost of not having the right crisis management software becomes visible not as an operational failure but as a compliance liability. The incident happened. The response happened. What cannot be proven happened, in the eyes of a regulator, effectively did not happen.
What This Looks Like in Practice
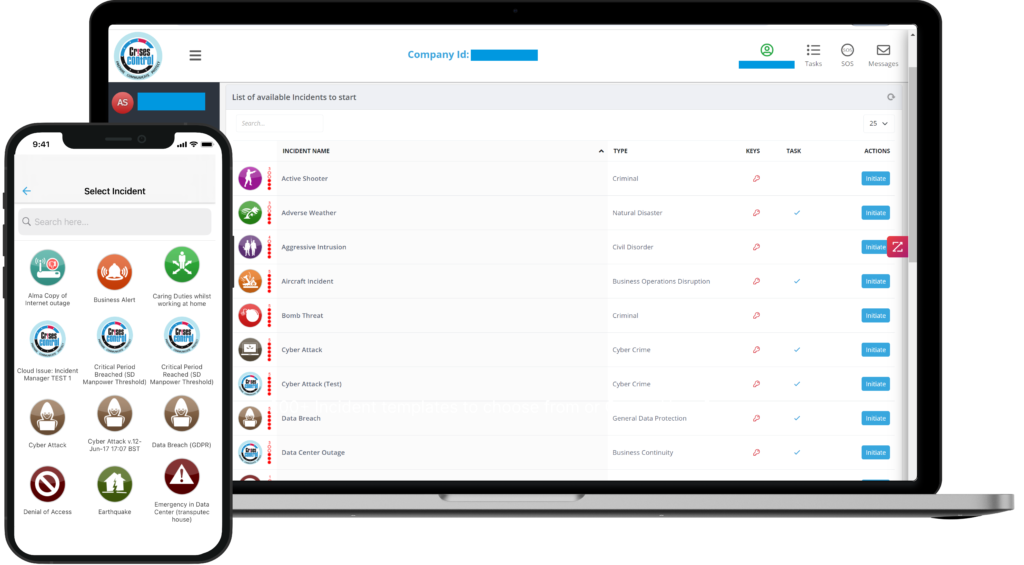
Crises Control is used by energy companies, utilities, and energy sector operators to close the gap between the alert and the structured, accountable response that follows it.
When an incident is logged, predefined workflows activate immediately across all sites involved. On-call engineers, HSE leads, site managers, external contractors, and regulatory notification contacts are all reached simultaneously through SMS, voice call, push notification, email, and Microsoft Teams. The system reaches people on satellite links, roaming networks, and basic mobile devices, not just smartphones on corporate plans.
Tasks are assigned to roles, not individuals, so shift changes and personnel unavailability do not create gaps in the response. The mass notification system tracks acknowledgement in real time and escalates automatically when a response is not received within the configured window.
Every action taken through the platform is time-stamped and logged automatically. By the time the incident closes, the audit trail that regulators, insurers, and legal teams will eventually need already exists as a complete record of the response.
The platform runs on its own cloud infrastructure with data centre coverage across the UK, Europe, North America, and the Middle East, including local hosting in Saudi Arabia, making it operationally independent of the corporate IT and OT systems that an energy sector incident may affect.
For energy companies evaluating options, user reviews on the Crises Control Capterra listing from operators in the energy and utilities sectors consistently point to notification reliability across multiple channels, speed of implementation, and the quality of real-incident support as the factors that differentiate the platform from alternatives that perform well in demos but fall short under operational pressure.
The Takeaway
Energy companies have invested heavily in monitoring and detection. The sensors are sophisticated. The alert systems work. The gap that persists is the 60 seconds after the alert fires, and the 60 minutes after that, when the response structure either holds or it does not.
What the energy sector needs from crisis management software is not better alerts. It needs the infrastructure that turns an alert into a coordinated, accountable, documented response: one that reaches the right people on the right channels regardless of the time or the state of the network, assigns ownership without manual intervention, communicates through a single channel that all parties can see, and builds the regulatory record automatically as the response unfolds.
Colonial Pipeline paid $4.4 million in ransom. The Halliburton breach cost $35 million. A Southeast Asian energy provider had its control systems disabled for 18 days. In each case, the initial detection was not the failure. The response infrastructure was.
The right crisis management software does not prevent every incident. But it ensures that when an incident occurs, the organisation has the structure to contain it, the communication to coordinate it, and the documentation to account for it. Explore how Crises Control supports energy sector organisations from the moment an alert fires through to post-incident review.
See what happens after the alert fires. Crises Control walks you through the platform against your specific sites, incident types, and regulatory obligations. Book a free personalised demo.
FAQs
1. What is crisis management software?
Crisis management software is a platform that coordinates everything after an alert fires, while alert systems only detect and notify. Crisis management software then assigns what those people must do, tracks that they have done it, escalates when they have not, maintains a shared operational picture across all parties, and builds the documented record that regulators and legal teams will eventually need. For energy companies, where incidents are complex, multi-party, and regulatory scrutiny follows every serious event, the distinction matters significantly.
2.What does emergency response software for the energy sector need to do that generic platforms do not?
Emergency response software for the energy sector must work in harsh conditions, across rotating shifts and multiple sites, in ways generic crisis tools are not designed for. Energy sector emergency response software needs to function on satellite links and roaming networks, handle rotating shift crews without individual-dependent task assignment, coordinate across internal teams and external agencies simultaneously, remain operational when corporate IT systems are compromised, and produce regulatory documentation that meets NERC CIP, FERC, OSHA PSM, or NIS2 requirements. These are not the default capabilities of a generic platform.
3. How is ransomware a crisis management problem, not just a cybersecurity problem?
Cybersecurity tools detect and block threats. When a ransomware attack succeeds, the crisis management problem begins: who is notified, in what order, through what channel, and with what instructions. Colonial Pipeline’s response was hampered because its communication and coordination infrastructure depended on the same IT systems that the ransomware had compromised. Crisis management software that runs independently of corporate systems remains operational precisely when the rest of the infrastructure does not. The detection is a cybersecurity function. The coordinated, documented, regulatory-compliant response is a crisis management function.
4.What compliance frameworks must crisis management software support for energy companies?
The minimum for US-based operators includes NERC CIP standards for grid operators, OSHA Process Safety Management for facilities handling hazardous chemicals, and the emerging CIRCIA mandatory reporting requirements for critical infrastructure. European operators must also meet NIS2 Directive requirements for cybersecurity and incident response. Cross-border operators face multiple overlapping frameworks simultaneously. The crisis management platform needs to produce documentation that satisfies each framework’s requirements, which means the audit trail must be timestamped, complete, and exportable in formats that regulators accept.
5.Why does infrastructure independence matter for energy sector crisis response software?
When Saudi Aramco was hit by the Shamoon cyberattack in 2012, the organisation was reduced to phone calls and faxes because the digital infrastructure for coordination was gone. Colonial Pipeline faced similar constraints during the 2021 DarkSide ransomware attack. Crisis response software that depends on the same corporate network, cloud environment, or IT infrastructure as the systems being attacked fails precisely when it is needed most. Independent cloud infrastructure with multi-region data centre coverage ensures the platform remains operational regardless of what the incident has done to the organisation’s own systems.

