Written by Dr Shalen Sehgal | Crises Control CEO
The week of April 7, 2026, delivered a masterclass in cyber catastrophe. Three major incidents hit within days of each other. First, CISA and the FBI issued joint advisory AA26-097A warning that Iranian-affiliated APT actors had compromised programmable logic controllers across US critical infrastructure, manipulating SCADA displays and causing operational disruptions. Then, a ransomware attack on ChipSoft paralysed electronic patient records across 70 percent of Dutch hospitals, forcing eleven facilities to take patient portals offline. In Massachusetts, Signature Healthcare’s Brockton Hospital diverted ambulances and cancelled chemotherapy treatments after attackers infiltrated their network.
Three sectors. Three continents. One common thread: the organisations that suffered most were not the ones with the weakest firewalls. They were the ones that could not communicate once the firewalls failed.
Most organisations have some form of incident response plan. Very few have a dedicated cyber attack emergency notification plan – one that works when email is down, when your network is compromised, and when regulators are counting the hours. That is the gap this post fills.
The Numbers That Should Keep You Up at Night
If the April 2026 incidents feel like outliers, the data says otherwise. The IBM Cost of a Data Breach 2025 report puts the global average breach cost at $4.44 million. In the United States, that figure jumps to a record $10.22 million, a 9 percent increase year over year. The average breach lifecycle sits at 241 days from detection to containment.
Ransomware is worse. The average cost hit $5.08 million in 2025, up 10 percent from the prior year. Only 12 percent of organisations that suffered a breach fully recovered. More than 75 percent took over 100 days to reach any meaningful recovery.
The one bright spot: organisations with incident response teams and regularly tested plans saved an average of $1.49 million per breach compared to those without. Preparation is a measurable financial advantage, not a compliance checkbox.
Healthcare is getting hit hardest. The HHS Office for Civil Rights logged 605 breaches in 2025, exposing 44.3 million people. Ransomware attacks across all sectors have surged 264 percent since 2018. And 53 percent of organisations report critical security staffing shortages, meaning fewer people are available to respond when the alarm sounds.
These are last year’s numbers. The question is not whether your organisation will face a cyber incident. It is whether you will be ready to communicate when it happens.
When Communication Breaks Down: Real-World Failures
Statistics tell you the scale. Case studies show you how it unfolds. In every major cyber incident of the last three years, communication failures amplified the damage far beyond what the attackers themselves achieved.
ChipSoft (April 2026): when silence forces shutdowns
When ransomware hit ChipSoft on April 7, 2026, it severed the digital lifeline connecting approximately 70 percent of Dutch hospitals to their electronic patient records. Z-CERT, the Netherlands’ healthcare Computer Emergency Response Team, immediately advised institutions to disconnect VPN connections and monitor for suspicious activity.
But the real damage came from the communication vacuum. Z-CERT publicly described difficult communication with ChipSoft in the critical first hours. Without clear information from the vendor, hospitals were left guessing about the scope of the compromise. Eleven hospitals disconnected patient portals, not because they were breached, but because nobody told them they were not.
Z-CERT Director Wim Hafkamp: “Digital outage is not an abstract IT problem. It concerns people who need care.” The absence of a proactive notification plan turned a single vendor attack into a nationwide healthcare disruption.
Change Healthcare (2024): the $3 billion communication collapse
The Change Healthcare breach remains the largest healthcare data breach in US history: 192.7 million people affected, total costs exceeding $3.09 billion by 2025. The ALPHV ransomware group exploited a Citrix portal lacking multi-factor authentication and exfiltrated six terabytes of data.
When Change Healthcare’s systems went down, they lost the ability to communicate with the thousands of healthcare providers who depended on them for claims processing. The American Medical Association found that 80 percent of affected physicians lost revenue from unpaid claims, 55 percent used personal funds to cover practice expenses, and 31 percent could not make payroll. The communication blackout lasted weeks. The financial ripple effects lasted months.
Colonial Pipeline (2021): panic from an information vacuum
When Colonial Pipeline shut down its fuel distribution network after a ransomware attack, the technical impact was significant but contained. What was not contained was the public response. The information vacuum created panic buying across the Eastern Seaboard, with queues and shortages that had nothing to do with actual supply constraints. Colonial paid a $4.4 million ransom, but the reputational and economic damage from the communication failure dwarfed that figure.
MOVEit (2023): the 72-hour deadline nobody met
The MOVEit Transfer vulnerability compromised over 2,500 organisations worldwide. Many were data processors with GDPR obligations to notify supervisory authorities within 72 hours. Notification responsibilities were unclear across the supply chain. Organisations did not know if they were the controller, the processor, or both. Dozens missed the regulatory deadline because they had no notification protocol that accounted for third-party breach scenarios.
The throughline across every case is the same: the actual breach damage was multiplied by communication failures. The attackers did not shut down communications. The organisations did it to themselves by having no out-of-band notification plan.
The Regulatory Notification Minefield
Cyber incident notification deadlines have tightened dramatically in the last two years. Regulators are enforcing them with real penalties.
Here are the timelines you are working against:
- DORA (EU financial entities): 4-hour initial notification to your competent authority after a major ICT incident is classified
- CISA (US federal agencies): 1-hour reporting window for confirmed cyber incidents
- GDPR Article 33: 72 hours to notify the supervisory authority after becoming aware of a personal data breach
- SEC (US public companies): 4 business days to file Form 8-K for material cybersecurity incidents
- HIPAA (US healthcare): 60 days to notify HHS when 500 or more individuals are affected
These deadlines are absolute. They do not pause because your email server is encrypted. They do not extend because your CISO is unreachable. They do not reset because it is a weekend.
In Q3 2025, Germany’s BaFin issued its first enforcement action under DORA, a EUR 450,000 fine for inadequate documentation of ICT third-party risk management. That was a documentation failure, not a breach. DORA requires three reporting stages: an initial notification within 4 hours, an intermediate report within 72 hours, and a final report within one month. If you are still figuring out who to call while your systems are down, you have already missed the first deadline.
The regulatory landscape makes one thing clear: you need a notification system that operates independently of your compromised infrastructure. Compliance cannot depend on the same network the attackers just took down.
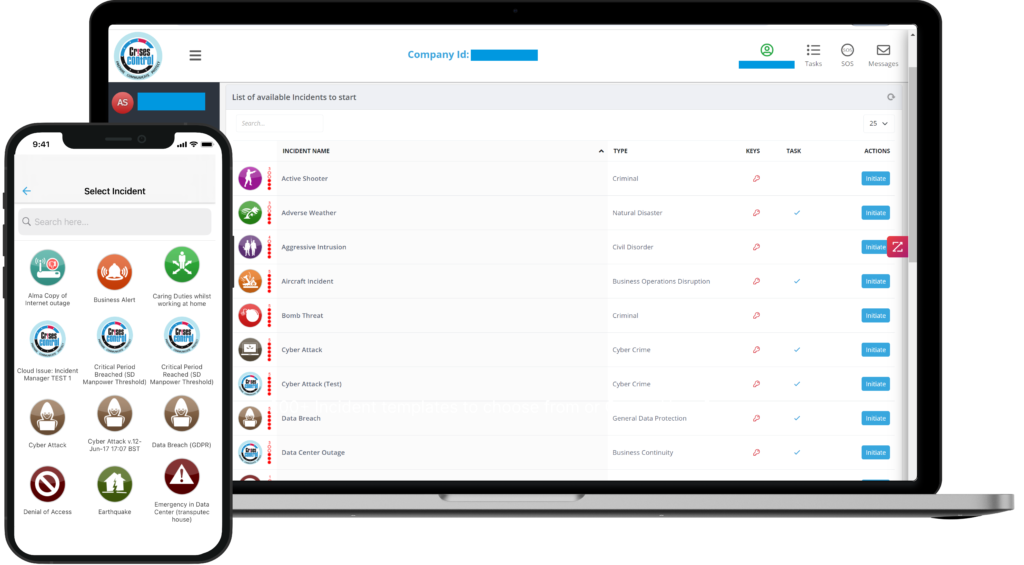
Interested in our Incident Management Software?
Flexible Incident Management Software to keep you connected and in control.
What a Cyber Attack Emergency Notification Plan Actually Looks Like
A proper cyber attack emergency notification plan operates in five distinct phases, each with specific actions, stakeholders, and communication channels.
Phase 1: detection and triage (0-15 minutes)
Your SIEM or monitoring platform detects anomalous activity and triggers an automated notification cascade. This is not the time for someone to manually look up phone numbers.
- Automated alert fires to the designated triage team via multi-channel delivery: SMS, voice call, and push notification simultaneously. Not email. Email may already be compromised.
- The triage team acknowledges receipt. Acknowledgement tracking is critical: you need to know who received the alert and who did not.
- Within minutes, the triage team confirms the severity level. Active ransomware or data exfiltration in progress is a Severity 1. A contained anomaly with low impact is a Severity 3.
- The confirmed severity level activates the corresponding playbook automatically.
Phase 2: internal escalation (15-60 minutes)
Once severity is confirmed, shift to role-based escalation. Not everyone needs to know everything immediately.
- Role-based notification trees: your SOC team gets technical details, legal counsel gets regulatory exposure assessment, your CEO gets a three-line status summary. Each role gets a different message, automatically routed.
- Pre-written message templates for each severity level: nobody should be wordsmithing under pressure. Templates are pre-approved by legal, reviewed quarterly, and loaded into your notification platform ready to deploy.
- Board and C-suite notification via a separate secure channel: if your corporate email is compromised, board communications must use an independent path.
- Incident command structure activates with assigned tasks. Each responder knows their role, their first three actions, and who they report to. Tasks are assigned and tracked automatically.
Phase 3: stakeholder and regulatory notification (1-72 hours)
This is where most organisations fall apart. The external notification obligations are complex, time-sensitive, and carry legal consequences.
- Regulatory authorities: notify per the timelines above. Your plan must pre-map which regulators apply to your organisation and have contact details and submission requirements pre-loaded.
- Customers and clients: deploy factual, pre-approved holding statements. State what you know, what you are doing, and when the next update will come. Do not speculate on scope.
- Insurance carrier and legal counsel: most cyber insurance policies require notification within a specific window. Miss it and you risk voiding coverage.
- Supply chain partners: if you are a vendor, your customers are making decisions in real time based on what you tell them. Proactive partner notification prevents the cascading shutdowns seen in the Dutch hospital crisis.
- Law enforcement: file with FBI IC3 and report to CISA. These steps are often forgotten in the heat of response but are critical for threat intelligence sharing and may be legally required.
Phase 4: ongoing communication (72+ hours)
Most breaches take weeks or months to fully resolve. Your notification plan must cover the long tail.
- Regular status updates at pre-set intervals: daily for Severity 1, every 48 hours for Severity 2. Remove ambiguity about when the next update will arrive.
- Internal updates to all employees: your staff will hear rumours and see media coverage. If you do not give them facts, they will fill the gap with speculation that will leak externally.
- Two-way acknowledgement tracking: every update should confirm who has received and read it. If your CFO has not acknowledged the latest status report, someone needs to follow up via an alternative channel.
Phase 5: post-incident review (30 days)
The incident is not over when systems come back online.
- After-action review with all stakeholders: what worked, what broke, where did the plan fail. Document everything.
- Update your notification plan: every incident reveals gaps. Close them while the experience is fresh.
- Regulatory follow-up reports: DORA requires a final report at one month. GDPR may require supplementary notifications if the scope of affected data expands.
- Audit trail documentation: every notification sent, every acknowledgement received, every escalation triggered, all timestamped and stored for compliance review.
Why Your Current Tools Will Not Cut It
You might be thinking: we have Teams, we have Slack, we have a phone tree. Here is why that is not enough.
Email servers may be the first thing attackers compromise or encrypt. Ransomware operators know that cutting email cripples response coordination. If your notification plan depends on Outlook, your notification plan dies with your Exchange server.
Collaboration tools like Microsoft Teams and Slack require network access and authentication infrastructure that may be unavailable during an attack. If Active Directory is compromised, Teams logins do not work. If your VPN is shut down as a containment measure, remote staff lose access to Slack entirely.
Phone trees are slow, unreliable, and produce no audit trail. A phone tree that reaches 500 people takes hours, depends on every person in the chain answering and passing the message correctly, and gives you zero proof that anyone received it. When BaFin or the ICO asks for evidence of your notification timeline, that is not a defensible answer.
What you actually need is a dedicated mass notification system built for crisis scenarios:
- Multi-channel delivery: SMS, voice, push notification, and desktop alert simultaneously. If one channel fails, others still reach your people.
- Automated escalation: if a critical responder does not acknowledge within the defined window, the system escalates automatically to their backup.
- Acknowledgement tracking: real-time visibility into who has received, read, and acknowledged each notification.
- Pre-loaded message templates: approved, tested, and ready to deploy in seconds.
- Complete audit trail: timestamped logs of every notification, every escalation, every acknowledgement, exportable for regulatory compliance.
- Cloud-based and infrastructure-independent: the platform operates entirely outside your corporate IT environment. When your network, email, and VPN are all down, your notification system is the one tool that still works.
The IBM statistic bears repeating: organisations with incident response teams and tested plans saved $1.49 million per breach. The plan is only as good as the tools that execute it. Mass notification for cybersecurity incident response bridges the gap between planning and execution.
How to Build Your Cyber Attack Notification Plan Today
You do not need six months and a consulting engagement to get started. Here is a practical checklist you can begin executing this week.
- Map yournotificationstakeholders.
Create a complete stakeholder register organised in tiers: Tier 1 is your incident response team, CISO, and CIO. Tier 2 is executive leadership, legal, HR, and communications. Tier 3 is regulators, customers, partners, and media. Every stakeholder needs a name, a role, a primary contact method, and a backup.
- Define severity levels with corresponding notification protocols.
Not every incident triggers the same response. A brute-force attempt on a non-critical system does not need board notification. Active ransomware encryption does. Define three to four severity levels and map each to specific notification tiers, message templates, and escalation timelines.
- Write pre-approved message templates for each scenario.
Create templates for ransomware, data breach, DDoS attack, insider threat, and third-party vendor compromise at minimum. Each template should include the incident type, known impact, actions being taken, and when the next update will be provided. Get legal sign-off in advance.
- Set up out-of-band communication channels.
Your notification system must work when your IT environment does not. That means a cloud-based platform delivering via SMS, voice, and push, with no dependency on your corporate network, Active Directory, or email servers.
- Integrate your SIEM and monitoring tools with your notification platform.
Automated triggering eliminates the human bottleneck. When your SIEM detects a critical event, the notification cascade should fire within seconds, not after someone reads an alert and starts looking up phone numbers.
- Test it quarterly.
Run cyber incident simulations that exercise your notification plan end to end. Simulate scenarios where email and VPN are unavailable. Measure time to first notification, percentage of stakeholders reached, and acknowledgement rates. Tested plans save money. Untested plans are fiction.
- Document everything for compliance.
Maintain audit trails of every test, every plan update, and every real-world activation. NIST SP 800-61 provides the gold standard framework for incident response documentation. DORA, GDPR, and SEC all require demonstrable evidence that your notification processes work. Your documentation is your defence.
Do Not Wait for a Breach to Find Out Your Plan Does Not Exist
The week of April 7, 2026, was not an anomaly. It was a preview. Iranian APT actors targeting critical infrastructure. Ransomware paralysing hospitals. Ambulances diverted from emergency rooms. These events will keep happening, and the organisations that recover fastest will not be the ones with the biggest security budgets.
They will be the ones who can still communicate when the firewalls fail.
The ChipSoft incident proved that a single vendor’s communication failure can cascade across an entire national healthcare system. The Change Healthcare breach showed that months of communication blackout cost billions. Every one of these incidents was made worse not by the attack itself, but by the inability to notify the right people, at the right time, through channels that actually worked.
Your cyber attack emergency notification plan is the difference between a controlled incident and an organisational crisis. Build it now. Test it quarterly. Make sure it runs on infrastructure the attackers cannot touch.
Get a free personalised demo of Crises Control to see how a purpose-built mass notification and incident management platform keeps your communication running when everything else goes down.
FAQs
1. What is a mass notification system for healthcare?
A mass notification system for healthcare is a communication platform designed to send urgent alerts to hospital staff, administrators, and stakeholders across multiple channels simultaneously, including SMS, push notifications, voice calls, email, overhead paging, and digital signage. Unlike generic notification tools, healthcare-specific systems support HIPAA-compliant messaging, role-based distribution, pre-built hospital code templates, two-way communication, and full audit trails required for regulatory compliance.
2.Is a mass notification system HIPAA compliant?
Not all mass notification systems are HIPAA compliant. A HIPAA compliant mass notification system must encrypt data in transit and at rest, support access controls, maintain audit logs of all communications, and prevent protected health information from being transmitted over unsecured channels. Consumer-grade messaging apps and standard group text services typically do not meet these requirements. Purpose-built platforms like Crises Control are designed with these compliance standards built in.
3.What are the CMS requirements for hospital emergency communication?
Under CMS Conditions of Participation (SS482.15), hospitals must maintain a documented emergency communication plan covering staff notification, coordination with external agencies, patient tracking during emergencies, and communication with patients’ families. The plan must be tested through annual exercises and produce documentation demonstrating compliance. The CMS Emergency Preparedness Rule applies an all-hazards approach, requiring communication systems that function across scenarios from natural disasters to cyberattacks.
4. How does a healthcare mass notification system differ from a standard one?
Healthcare mass notification systems differ from standard platforms in several key ways: they support pre-built hospital code alerts (Code Blue, Code Silver, Code Red), enable role-based messaging so different teams receive tailored instructions during the same incident, integrate with clinical systems like nurse call and EHR platforms, maintain HIPAA-compliant audit trails, and operate independently of internal IT infrastructure so they function even during cyberattacks or system outages.
5.Can a mass notification system integrate with hospital paging and nurse call systems?
Yes. Advanced healthcare mass notification platforms integrate with hospital paging systems, nurse call systems, building management systems, fire alarm panels, access control systems, and electronic health records. These integrations enable automated alert triggering. For example, a fire alarm activation can automatically initiate a Code Red notification across all channels without manual intervention, significantly reducing response times.

