Written by Dr Shalen Sehgal | Crises Control
ISO 22301 is the international standard for business continuity management systems, setting out exactly what an organisation has to do to keep critical operations running when something goes wrong and to prove it did so when an auditor asks. It is built around six requirements: leadership commitment, risk and impact analysis, documented response plans, defined roles, regular testing, and a continuous audit trail.
For food manufacturers, ISO 22301 has a sharper edge. It is the standard that retailer technical agreements, retailer audits, and, increasingly, insurers expect to see in place. Failure to maintain it does not just risk certification; it risks contracts. The average UK food recall already costs an estimated 6 million pounds before reputational damage is counted (Food Manufacture / GS1 UK 2023), and the audit gap is where most of that cost gets locked in.
What is ISO 22301 for food manufacturers?
ISO 22301 for food manufacturers is the business continuity management standard applied to food production, covering contamination, recall, supply chain failure, and safety events. It requires documented plans, named roles, multi-channel notification, regular testing, and a continuous audit trail that aligns with HACCP and BRCGS workflows.
It is Tuesday morning at a chilled prepared-foods plant in the Midlands. The BSI auditor sits down with the technical director and asks a single question: show me the evidence. Not the plan, the evidence. Every alert sent during the listeria swab incident in March, every acknowledgement received, every decision logged with a timestamp, every task completed, every retailer notification timed against the window.
The plan exists. It is on the shared drive. The technical director scrolls through emails, group chat exports, and a partially completed post-incident review form. Three hours later, the auditor closes the meeting with a major non-conformance. The certification is deferred. The largest retailer’s customer technical team is informed within 48 hours under contract terms. The site is given six months to close the gap.
ISO 22301 audits in food manufacturing fail for one reason more than any other. No defensible audit trail when something actually goes wrong.
Why ISO 22301 is harder for food manufacturers than other sectors
Most published guidance on ISO 22301 is written for office-based organisations. Banking. Insurance. Professional services. The standard reads cleanly when applied to those environments. Food manufacturing breaks the assumptions on the first page.
Production runs across three shifts, seven days a week, with seasonal contractors, agency staff, and third-party hauliers who are not on the regular HR system. The people most likely to first detect a continuity-relevant event, whether a contamination swab, a utility failure, or a supplier delivery problem, are not the people sitting at desks watching their email. The chain of custody on every batch is regulated independently of business continuity. Every minute of confusion adds to the recall window. The cost is not just downtime; it is product on shelves that has to come back.
There is also the matter of who needs to know, and how fast. A continuity event in food manufacturing triggers obligations to the Food Standards Agency, retailer technical teams, environmental health officers, the head office, the brand team, and often the public, all on different timelines defined by hazard category. None of those obligations can be evidenced from a shared drive after the fact.
UK food businesses issued 1,386 product recalls and withdrawals between 2019 and 2023, with allergen and pathogen contamination as the two leading causes (Food Standards Agency 2024).
The 6 evidence categories ISO 22301 requires from food manufacturers
ISO 22301 certification rests on six categories of evidence. Each one has to be defensible under audit, and each one is where most food manufacturing sites have a gap.
1. Leadership commitment and policy
Documented evidence that senior leadership has signed off on the business continuity policy, allocated resources, and integrated it into the management system. This is the easiest category to evidence on paper and the one most often disconnected from operational reality. Auditors increasingly cross-check leadership sign-off against actual exercise participation. A signature on a policy that the signatory has never tested is a finding.
2. Risk assessment and business impact analysis
A documented risk assessment that identifies disruption scenarios specific to the site, with a business impact analysis defining the maximum tolerable period of disruption for each critical function. For food manufacturing, this has to align with the existing HACCP plan and the BRCGS standards. Generic BIAs that ignore site-specific food-safety triggers are the most common reason this category fails.
3. Documented response plans with named roles
Plans for each disruption scenario, with named roles, deputies, and escalation paths. Not generic role names, named individuals with documented backups. Plans that name a single technical director with no deputy fail this category as soon as the auditor asks what happens when that person is unreachable. Single points of contact are the most common failure mode in food manufacturing continuity events.
4. Multi-channel notification with confirmation
Evidence that the organisation can reach all relevant personnel across multiple channels, with two-way confirmation. SMS, voice, email, push, and app, with timestamped acknowledgement. Email-only setups fail this category by default. Phone-tree setups fail because they cannot evidence acknowledgement timing.
A signature on a policy is not a commitment. A signature against a logged exercise is. Auditors have learned the difference.
5. Regular testing under realistic conditions
Documented exercises that test the plan under conditions resembling a real incident. Tabletop sessions where everyone is in the same room with coffee do not count. Auditors increasingly want to see live exercises with multi-shift participation, contractor inclusion, and timed responses. The exercise log has to show what worked, what failed, and what was changed as a result.
6. Continuous audit trail captured automatically
This is where most food manufacturing sites fail. Every alert, every acknowledgement, every escalation, every decision, every task, and every retailer notification is captured automatically against a timestamp. That trail is what the BSI auditor, the FSA, the retailer technical team, and ISO 22301 itself require. Without it, the response cannot be evidenced. With it, the site can demonstrate every regulatory and contractual obligation in a report rather than a forensic exercise.
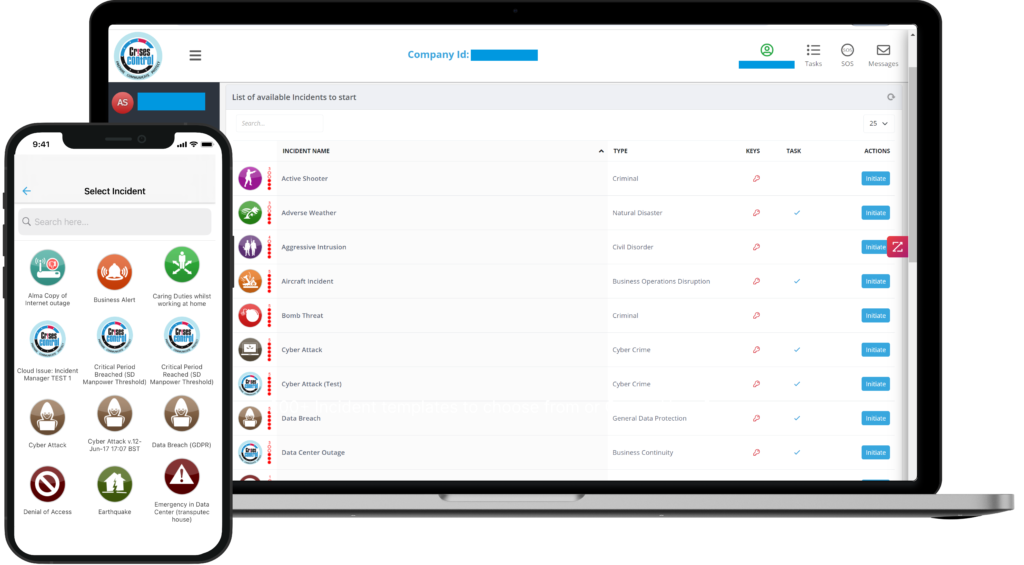
Interested in our Incident Management Software?
Flexible Incident Management Software to keep you connected and in control.
Why most food manufacturing ISO 22301 audits surface the same gap
Three patterns show up across food manufacturing post-audit reviews. The plan exists, but the evidence does not. The evidence exists, but it is reconstructed from email and memory after the fact. The reconstruction is good enough for a first certification, but not for a renewal under a stricter auditor or after a real incident.
The deeper issue is that most setups were never designed to generate evidence as a by-product of running the response. They were designed for the audit, then asked to handle a real listeria swab at 03:22 on a Tuesday. The two requirements pull in opposite directions, and under pressure, the audit-first design always loses to the operational-first reality.
Before and after: what closing the audit gap changes
The difference between a manual evidence chain and a platform-based audit trail shows up in measurable certification outcomes.
|
Audit factor |
Manual evidence chain |
Platform-based audit trail |
|
Time to produce audit evidence |
Days, often incomplete |
Minutes, exportable on demand |
|
Notification acknowledgement timing |
Reconstructed from email |
Captured automatically |
|
Decision logging |
Memory and meeting minutes |
Timestamped at the moment |
|
Exercise documentation |
Manual write-ups, often skipped |
Generated from the exercise itself |
|
Retailer technical agreement evidence |
Pieced together post-event |
Available in real time |
|
Risk of major non-conformance |
High at renewal |
Materially reduced |
How Crises Control closes the ISO 22301 audit gap for food manufacturers
Most competitors either notify people or document plans. Crises Control executes the response. Built for real incidents, not demos.
Mass notification platforms like Everbridge, OnSolve, and AlertMedia handle alerts well. They get the message out. They do not generate the continuous audit trail that ISO 22301 requires across every phase of an incident. Planning platforms like Fusion and Riskonnect are strong on the document side, but they were not built for the live, time-pressured floor of a food manufacturing incident, and their audit trail depth depends on what users remember to log. Teams and Slack are useful for everyday work and useless under audit.
Crises Control is the platform that generates ISO 22301 audit evidence as a by-product of running the response across notification, coordination, task ownership, and reporting. It is also the platform behind which Crises Control itself holds ISO 22301 accreditation, so the standard is built into the product, not bolted on after.
How Crises Control compares against the alternatives
|
ISO 22301 evidence requirement |
Manual setup |
Notification tools |
Planning tools |
Crises Control |
|
Continuous timestamped audit trail |
No |
Partial |
Partial |
Yes |
|
Multi-channel notification with confirmation |
No |
Yes |
No |
Yes |
|
HACCP and BRCGS aligned workflows |
Partial |
No |
Yes |
Yes |
|
Named roles with deputies and escalation |
Partial |
Partial |
Yes |
Yes |
|
Exercise evidence captured automatically |
No |
No |
Partial |
Yes |
|
Vendor itself ISO 22301 certified |
N/A |
Varies |
Varies |
Yes |
Business continuity workflows aligned to ISO 22301
The Crises Control business continuity platform turns the standard into a live workflow. Every clause that requires evidence is mapped to a platform action, and every platform action generates the evidence automatically. The technical team stops doing two jobs.
Mass notification with confirmed acknowledgement
The Crises Control mass notification system reaches floor staff, technical teams, leadership, and external stakeholders across SMS, voice, email, push, and app, with two-way confirmation. The audit trail captures who acknowledged, when, and on which channel. That is what the BSI auditor wants to see, in seconds, not days.
Incident management with named owners and timed escalation
The incident manager turns each disruption scenario into a live workflow. Each phase has named owners, deputies, escalation paths, and pre-built actions that match the site’s existing HACCP and BRCGS protocols. Decisions get logged with timestamps as they happen, so the post-incident review is generated rather than reconstructed.
Audit trail that holds up under BSI, FSA, and retailer review
Every alert, acknowledgement, decision, task, and message is captured automatically in the Crises Control audit trail. When the BSI auditor, the FSA, or the retailer technical team ask what happened and when, the answer is exportable in minutes, against timestamps, by clause.
If your current setup would not produce a defensible audit trail under a six-hour BSI review, it is time to test it under real conditions. Book a demo to see it run.
What working ISO 22301 looks like in a food manufacturing site
A working setup is short enough to operate from a phone on the floor and structured enough to generate the evidence ISO 22301 requires without anyone consciously generating it. It names roles, not people. It assumes the named lead is unreachable and defines the deputy. It uses multiple channels because no single channel works in every incident. It captures everything, because regulators, retailers, and the BSI auditor will all ask. And it gets tested in conditions that mirror the real thing, with evidence captured by the system rather than typed up afterwards.
Sites that adopt this approach do not just pass ISO 22301 audits. They turn audit week from a fire drill into a report run. The contamination still happens. The non-conformance does not.
If your ISO 22301 audit trail is currently a shared drive and a memory of who sent what, the next renewal is already at risk. Book a demo of the platform.
FAQs
1. What does ISO 22301 require from a food manufacturer?
ISO 22301 requires a food manufacturer to operate a documented business continuity management system covering leadership commitment, risk and impact analysis, response plans with named roles, multi-channel notification, regular testing, and a continuous audit trail. For food manufacturing, the system must align with HACCP, BRCGS, and the site’s regulatory and retailer obligations. Certification is awarded by accredited bodies such as BSI after a multi-stage audit.
2. Why do food manufacturing sites fail ISO 22301 audits?
The most common failure is the audit trail. The plan exists, the policy is signed, the team has been briefed, but the evidence of what actually happened during real incidents and exercises is reconstructed from email and memory rather than captured automatically. Auditors increasingly treat reconstruction as a major non-conformance, especially at certification renewal.
3. Does ISO 22301 replace HACCP or BRCGS?
No. ISO 22301 is the business continuity layer that runs alongside food safety standards, not instead of them. HACCP defines the food safety controls. BRCGS defines the food safety management system. ISO 22301 ensures that when something goes wrong with either, the response is structured, documented, and reversible. The three should reinforce each other, with the continuity workflows referencing HACCP triggers and BRCGS protocols directly.
4. How long does ISO 22301 certification take in food manufacturing?
A first-time certification typically takes between six and twelve months, covering gap analysis, plan documentation, exercise programmes, and stage-1 and stage-2 audits with an accredited body. Sites with platform-based business continuity tooling generally complete the cycle faster because the evidence is generated as a by-product of normal operations rather than assembled separately.
5. What evidence does ISO 22301 software produce for a BSI audit?
A complete audit trail covering every alert sent, every acknowledgement received, every escalation triggered, every decision logged, every task completed, every exercise run, and every retailer notification timed against contractual windows, all against timestamps. This trail is what the BSI auditor and the retailer technical team ask to see. Setups that cannot produce it on demand are exposed at the next certification cycle.

