Organisations face the constant challenge of managing and mitigating system incidents efficiently with the increase of digitalisation. These incidents, ranging from IT disruptions to security breaches, can have severe consequences if not handled promptly and effectively. In this blog, we look into the intricacies of system incident management, shedding light on how it works and how Crises Control emerges as the ultimate ally.
Understanding System Incident Management
Defining System Incident Management
System Incident Management is a comprehensive approach to identifying, analysing, and resolving disruptions in an organisation’s IT infrastructure. This process involves a structured set of activities aimed at restoring normal operations swiftly, minimising the impact on business processes.
The Core Components
Effective incident management comprises key components, including incident detection, reporting, analysis, response, and learning. These components work cohesively to create a robust incident management framework.
The Crises Control Advantage
Holistic IT Incident Management Solutions
Crises Control, a leader in the field, offers a holistic approach to IT incident management. Our platform seamlessly integrates with your existing systems, providing real-time incident detection and automated reporting. This ensures that potential issues are identified promptly, allowing for a proactive response.
Tailored Incident Response Plans
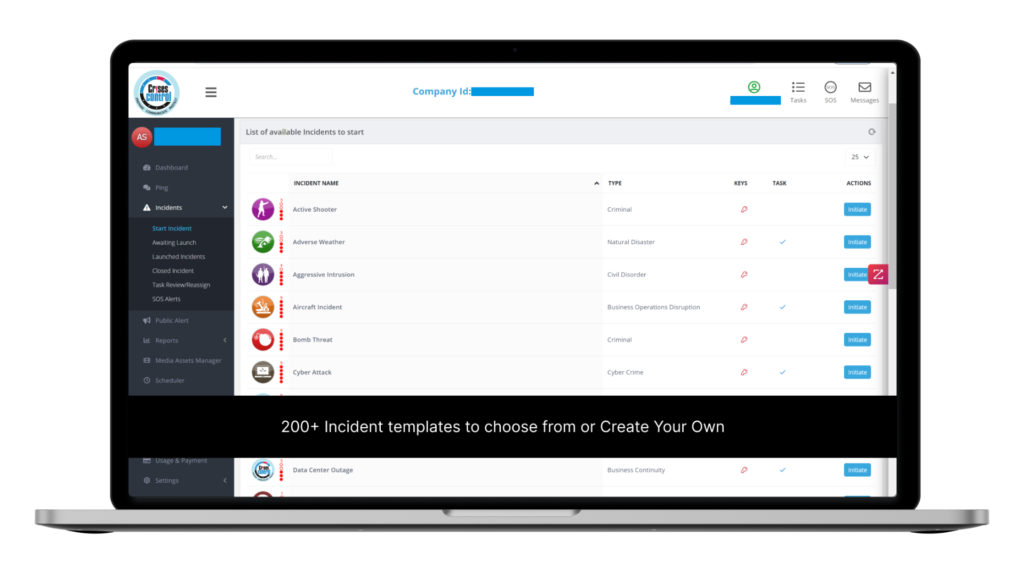
One size does not fit all when it comes to incident response. Crises Control understands this, offering customisable incident response plans tailored to the unique needs of your organisation. This flexibility ensures that your team is equipped to handle any incident effectively. Crises Control offers extensive customisation options to adapt its solutions to the unique needs of your organisation. Here’s how it can be customised:
- 1. Tailored Incident Response Plans:
- Crises Control allows you to create incident response plans specific to your organisation’s structure and requirements.
- Customise workflows, actions, and communication channels to align with your established protocols.
- 2. User Permissions and Roles:
- Define and customise user roles and permissions based on your organisational hierarchy.
- Ensure that the right individuals have the appropriate access and authority during incidents.
- 3. Alerts and Notifications:
- Customise alert parameters to match your organisation’s urgency levels and escalation processes.
- Specify who receives notifications, how, and when, ensuring a personalised alert system.
- 4. Integration with Existing Systems:
- Seamlessly integrate Crises Control with your existing IT infrastructure.
- Customise the integration to work cohesively with your current tools and technologies.
- 5. Data Capture and Analysis:
- Tailor data capture forms to gather information relevant to your organisation’s specific incidents.
- Leverage customisable analytics to derive insights specific to your incident management goals.
- 6. Training and Simulation:
- Customise training modules and simulations to mimic the unique challenges your organisation may face.
- Ensure that your team is well-prepared for incidents specific to your industry and operational environment.
- 7. User Interface Preferences:
- Personalise the user interface based on the preferences and requirements of your team members.
- Adapt the layout and features to enhance user experience and efficiency.
- 8. Compliance and Reporting:
- Customise compliance reporting to meet the regulatory requirements of your industry.
- Generate reports tailored to your organisation’s specific incident management metrics.
Navigating the Incident Management Landscape
Real-Time Incident Detection
Crises Control’s cutting-edge technology enables real-time incident detection. Through advanced monitoring and alert systems, potential disruptions are identified as they occur, allowing for immediate action.
Automated Incident Reporting
Manual incident reporting can be time-consuming and prone to errors. Crises Control automates this process, ensuring that all stakeholders receive accurate and timely information. This automation not only saves valuable time, but also reduces the risk of misinformation.
The Incident Management Lifecycle
Analysis for Informed Decision-Making
Crises Control empowers organisations with in-depth incident analysis capabilities. Through detailed insights and analytics, decision-makers gain a comprehensive understanding of the incident, facilitating informed responses and long-term improvements.
Efficient Incident Response
With predefined response plans and automated workflows, Crises Control streamlines the incident response process. This efficiency is crucial in minimising downtime and maintaining the integrity of your operations.
Crises Control: Your Partner in Incident Management Success
Proactive Learning and Adaptation
Crises Control goes beyond incident resolution. The platform facilitates proactive learning and adaptation by capturing and analysing data from each incident. This information is invaluable in refining incident response plans and preventing future occurrences.
User-Friendly Interface
Designed with the end-user in mind, Crises Control boasts an intuitive and user-friendly interface. This ensures that even non-technical personnel can navigate the platform seamlessly, contributing to a more efficient incident management process.
Empower Your Organisation with Crises Control
Mastering system incident management is pivotal in safeguarding your organisation against the unpredictable nature of today’s digital landscape. Crises Control emerges as the go-to solution, offering a robust and comprehensive platform that not only addresses incidents promptly, but also empowers organisations to learn and adapt continuously.
Take the first step towards incident management excellence. Contact us today to schedule your free demo and experience the power of Crises Control firsthand. Your organisation’s resilience starts here.
FAQs
1. What is System Incident Management, and why is it crucial for businesses?
System Incident Management is a structured approach to identifying, analysing, and resolving disruptions in an organisation’s IT infrastructure. It is crucial for businesses because it helps minimise the impact of incidents, ensuring swift recovery and maintaining the integrity of business processes.
2. How does Crises Control’s incident detection differ from traditional methods?
Crises Control employs advanced real-time incident detection technology, which distinguishes it from traditional methods. Through continuous monitoring and alerts, potential disruptions are identified as they occur, enabling a proactive response and reducing the risk of prolonged downtime.
3. Can Crises Control adapt to the unique needs of my organisation’s incident response?
Yes, Crises Control offers customisable incident response plans tailored to the specific needs of your organisation. This flexibility ensures that your team is equipped to handle diverse incidents effectively, providing a personalised and efficient approach to incident management.
4. How does Crises Control contribute to proactive learning in incident management?
Crises Control goes beyond incident resolution by capturing and analysing data from each incident. This information is then used for proactive learning, facilitating continuous improvement in incident response plans and helping prevent future occurrences.
5. Is Crises Control suitable for non-technical personnel?
Absolutely. Crises Control is designed with a user-friendly interface, making it accessible and intuitive for both technical and non-technical personnel. This ensures that all team members can navigate the platform seamlessly, contributing to a more efficient and inclusive incident management process.








